uniFLOW Online in Zero Trust environments
You can’t move without someone mentioning “Zero Trust” networks. According to Microsoft, 96% of security decision-makers state that Zero Trust is critical to their business’ success with 76% already adopting Zero Trust security measures1.
What does Zero Trust network mean?
Zero Trust is no fixed model; supporting Zero Trust isn’t a “one size, fits all” solution. Every business can and will implement the ideas of Zero Trust in a way that suits their organization at the time. Thus, Zero Trust needs to adapt to the security architecture implemented by the customer while they progress along their journey towards a Zero Trust network. This may mean that the customer will start with one network and security architecture then slowly transition to their final implementation model over time. uniFLOW Online follows the Zero Trust principles defined by Microsoft:
- Verify explicitly
- Use least privilege access
- Assume breach
uniFLOW Online provides many implementation options which allow the customer to decide which one works for their network regardless of where they are on the Zero Trust journey.
uniFLOW Online – following the “verify explicitly” principle
Firstly, let’s look at the consistent parts regardless of how they will be implemented. uniFLOW Online is built with a “security first” focus, so all communication is authenticated before any functions can be carried out. Users log in using their existing company credentials such as Microsoft 365, Google Workspace, OKTA, and many more, in line with any multi-factor authentication policies defined by the IT department. This is part of the “verify explicitly” Zero Trust principle.
uniFLOW Online – following the “use least privilege access” principle
Once the user has been identified, they can only perform actions they are entitled to do as part of their job. Most users will only be allowed to print, scan and copy on the devices they have been granted access to. A fleet manager will be given privileged access to manage the printers themselves but probably not provided with personal details as this function is reserved for other network admins. In a school, college or university environment, some staff may also handle cash and oversee users’ budgets. Other people can be granted a mix of rights, depending on their job requirements. This is part of the “use least privilege access” principle.
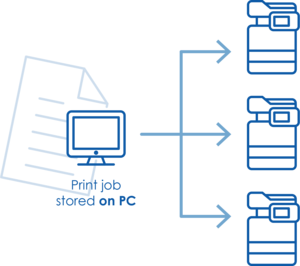
Zero Trust in small office locations
For some customers, it may be that users’ PCs and printers are on the same network and can all talk to each other. This does not prevent lateral movement from one device to another, so it may not follow the “assume breach” principle. On the other hand, it might be because the business hasn’t moved to a more secure level of network isolation yet or simply that it is a small office with only a few network points. Whatever the reason, uniFLOW Online can work with this customer network type by storing the jobs on user’s PCs and releasing them directly to the printer when required.
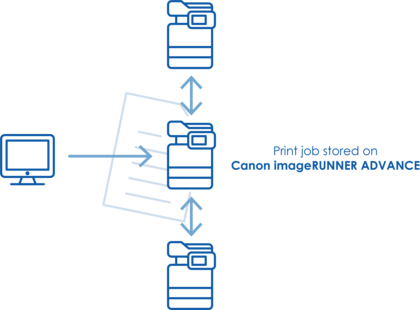
Zero Trust in offices with a firewall or network restrictions
There might be firewall or virtual network restrictions between the PCs and printers for more secure implementation. uniFLOW Online can work with this network implementation by storing the jobs on the Canon imageRUNNER hard disk. A print job can be sent directly from a multi-functional device to a multi-functional device if a user wishes to release it on a different device. This also avoids the problem of the print job not being available if the user’s PC is turned off when they want to release their job.
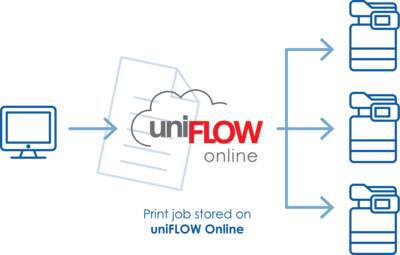
Zero Trust in networks with micro-segmentation
The final, most secure, and increasingly more common approach, is to have every network point isolated from each other regardless of the type of device. In this network configuration, each device can only talk to the Internet i.e. there is no lateral movement of any form on the local network. The network’s micro segmentation is the best form of “assume breach” Zero Trust principle. Naturally, uniFLOW Online can work seamlessly in this customer environment; all secure print jobs are stored in the cloud. The Canon devices then pull the jobs down directly once a user has identified and selected which jobs they want to release. Users can also use their mobile phone to release jobs simply by scanning a QR-code on the device UI. And if necessary, uniFLOW Online supports direct printing in micro segmented networks. The Canon device only needs a power supply and a network cable. No other infrastructure or services of any kind are required.
[1] www.microsoft.com/security/blog/2021/07/28/zero-trust-adoption-report-how-does-your-organization-compare/